Mar 21, 2026 · 5 min read
7,500 Online Stores Got Hacked Through the Same Magento Flaw—Including Toyota and FedEx
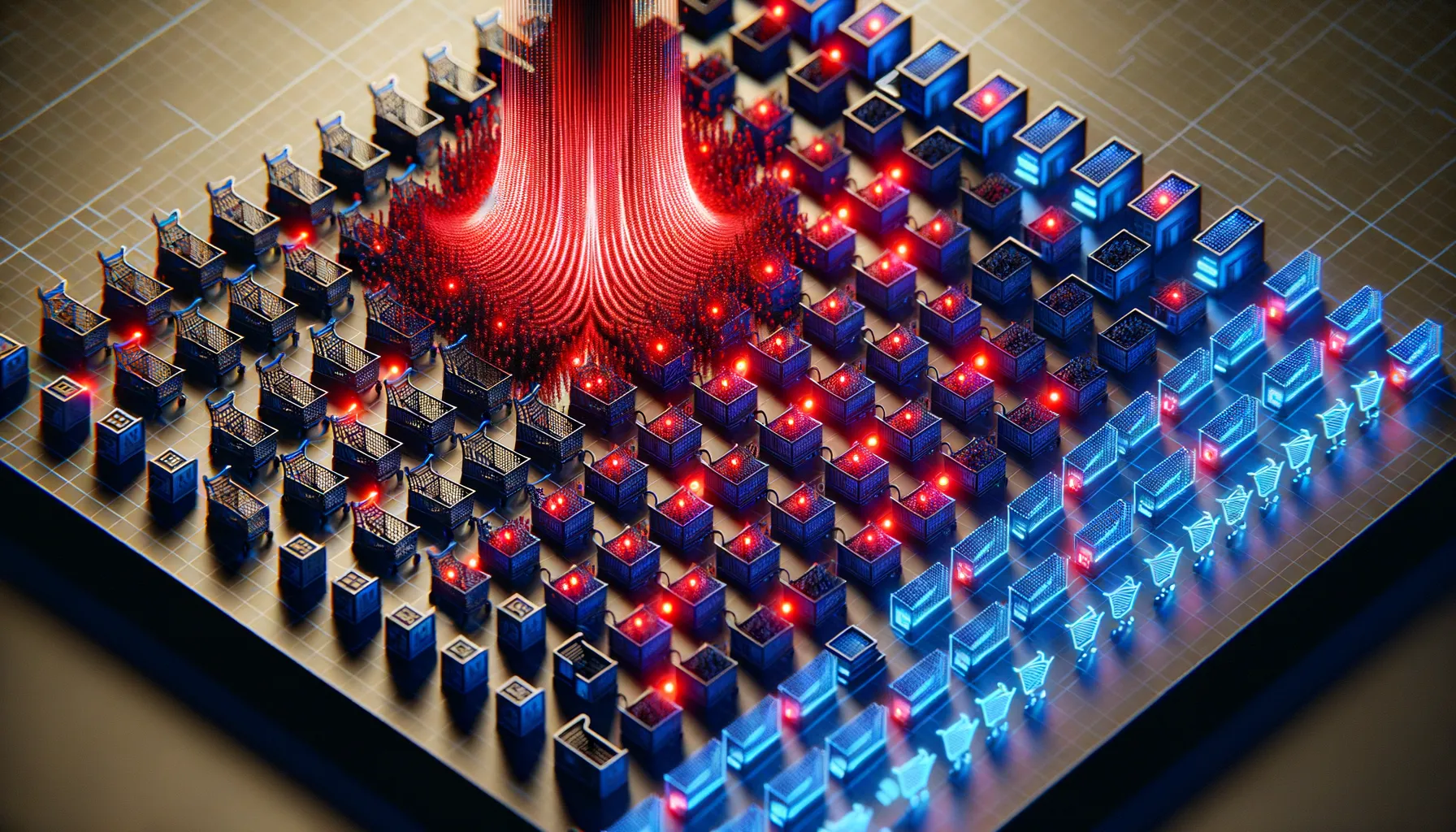
An unauthenticated file upload vulnerability in Magento let attackers deface 7,500 ecommerce sites across 15,000 hostnames. The hackers left graffiti this time. Next time, it could be payment skimmers.
Starting February 27, 2026, attackers began systematically uploading files to Magento powered websites. Within three weeks, they had compromised approximately 7,500 domains across more than 15,000 hostnames, including infrastructure associated with Toyota, Fiat, Asus, Bandai, FedEx, government agencies, and universities. Netcraft's digital risk protection platform documented the campaign as it unfolded.
This particular wave of attacks was mostly vandalism. The hackers uploaded text files displaying their handles and bragging rights. But the vulnerability they exploited, an unauthenticated file upload flaw, could just as easily be used to inject payment card skimmers, cryptocurrency miners, or redirect scripts into online stores. The defacement is the warning shot. The real threat is what comes next.
How the Attack Works
Researchers identified the attack vector as an unauthenticated file upload vulnerability affecting multiple Magento editions. The flaw was confirmed on Magento Community 2.4.9 beta1, but evidence suggests it impacts Magento Open Source, Enterprise, and B2B editions as well.
"Unauthenticated" is the critical word. Attackers do not need a login, an admin password, or any credentials at all. They simply upload a file to a publicly accessible directory on the server. The uploaded content becomes immediately accessible through a web browser, and on a vulnerable Magento installation, there is nothing stopping them.
The simplicity of the attack is what makes the scale possible. With a script that scans for Magento installations and attempts the upload, a single attacker can compromise thousands of sites in hours.
Who Was Hit
The campaign was opportunistic, targeting any reachable Magento installation rather than specific companies. But the list of affected organizations reveals just how widely Magento is deployed:
- Major brands: Toyota, Fiat, Asus, Bandai, FedEx
- Government domains in Latin America and Qatar
- Universities running ecommerce portals
- Nonprofit organizations
- Trump Organization domains
Most affected sites were subdomains, staging environments, or regional offices. However, some production ecommerce sites experienced brief compromise before the defacement was noticed and removed.
Why Defacement Is Just the Beginning
The attackers behind this campaign, using handles like L4663R666H05T, Simsimi, Brokenpipe, and Typical Idiot Security, were motivated by notoriety within the defacement community. They self reported their exploits to Zone-H, a defacement archive, and left "greetz" messages typical of hackers seeking reputation rather than profit.
But the vulnerability they exploited does not care about the attacker's motivation. The same unauthenticated file upload that allows a text file to be placed on a server also allows a JavaScript payment skimmer to be injected into checkout pages. Magecart attacks, named after Magento, have stolen millions of credit card numbers through exactly this type of vulnerability. The technique has been the foundation of ecommerce cybercrime for nearly a decade.
When defacement groups find and publicly exploit a vulnerability, financially motivated criminals take notice. The defacement campaign essentially published a roadmap showing which sites are vulnerable and how to get in.
The Magento Problem
Magento, now known as Adobe Commerce, powers hundreds of thousands of online stores worldwide. Its popularity makes it a persistent target. When a single vulnerability affects the platform, it creates a "force multiplier" effect where attackers can automate exploitation at massive scale.
This is not the first time Magento has been at the center of a mass compromise. The platform has a long history of being targeted by Magecart groups, and the transition from Magento 1 to Magento 2 left many stores running outdated, unpatched versions. Staging environments and development instances, which are often less carefully secured, provide easy entry points that attackers can use to pivot into production systems.
What This Means for Online Shoppers
If you shop online, there is a good chance some of the stores you use run on Magento. You cannot easily tell from the outside whether a store has been patched, but you can reduce your exposure:
- Use virtual credit cards. Services like Privacy.com let you create single use card numbers that limit your exposure if a store's checkout page has been compromised.
- Watch for checkout anomalies. If a familiar store's checkout page looks different, loads slowly, or redirects you to an unfamiliar domain, do not enter your payment details.
- Prefer established payment methods. Apple Pay, Google Pay, and PayPal do not expose your actual card number to the merchant, which means a compromised checkout page cannot steal it.
- Monitor your statements. Check your credit card statements regularly for small unauthorized charges. Skimmer operators often test stolen cards with small transactions before making larger purchases.
For Store Operators
If you run a Magento based store, the defacement campaign is a direct signal that your platform may be vulnerable:
- Check for unauthorized files in publicly accessible directories immediately
- Apply the latest Adobe Commerce security patches
- Audit staging and development environments, which were disproportionately affected in this campaign
- Implement file integrity monitoring to detect unauthorized uploads
- Review server logs for the attacker handles associated with this campaign
The defacement groups did you a favor by making their presence obvious. The next attackers will not be so considerate.