Apr 30, 2026 · 6 min read
A Hacker Just Posted 6.8 Billion Email Addresses to BreachForums—And Researchers Confirmed 3 Billion of Them Are Real
A user calling himself "Adkka72424" published a 150 GB compilation he says he spent two months building from infostealer logs, credential stuffing combos, and breach databases. Cybernews stripped duplicates and invalid entries and still landed on roughly 3 billion working addresses. The world has 5.5 billion email users.
Six Billion Lines, Two Months of Stitching
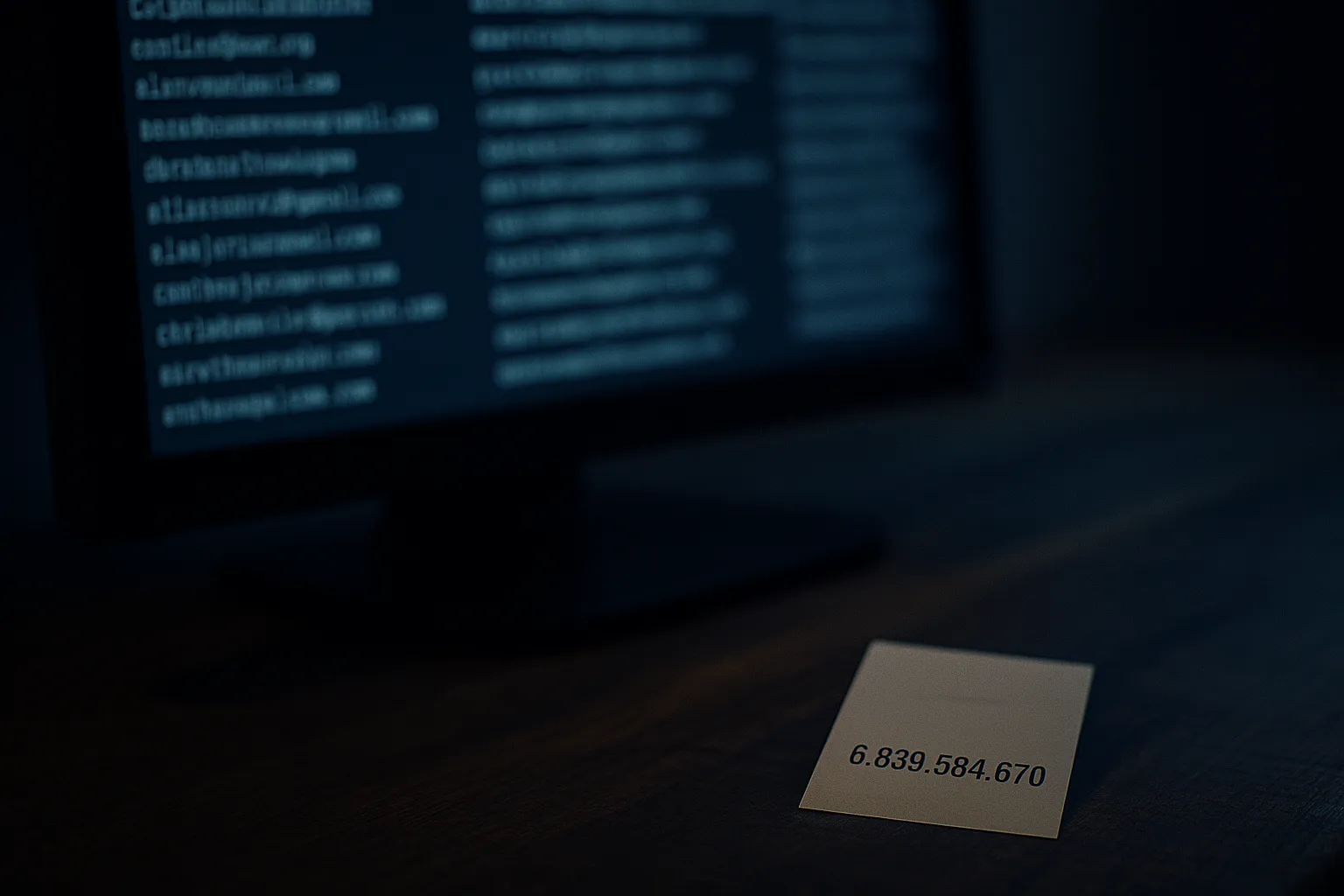
The dump landed on BreachForums under the handle Adkka72424. The post was blunt about the source. Per the threat actor's own statement, quoted by Cybernews researchers: "Two years ago, I obtained more than 3.3 billion unique email addresses. After a long break, I started this again and spent about 2 months extracting emails from various combos, ULP collections, logs, and databases and extracted 6,839,584,670 unique email addresses."
Translation: this is not a single fresh hack of Gmail or Yahoo. It is a meta compilation. The hacker scraped credential combo lists, infostealer dumps from devices infected with malware, and the residue of older breaches, then deduplicated the set into a single 150 GB file.
The number on the title is 6.8 billion. The number that matters is the one Cybernews verified after de duplication and sanity checks. According to TechRadar's analysis of the dump, roughly 3 billion of the addresses are unique, valid, and reachable. Set against the 5.5 billion people on Earth who use email at all, that's a near majority public exposure.
Why Aggregations Are Worse Than Single Breaches
It's tempting to dismiss this as "old data." Most of the addresses leaked years ago in other breaches—LinkedIn, MyFitnessPal, Adobe, the Collection #1 dump from 2019. The phrase "your data is public" is doing a lot of work in that defense.
The aggregation problem is what changes the threat. A single 2019 breach exposed your email next to one site's password. The Adkka72424 dump exposes your email next to a unified profile that any threat actor can cross reference with newer infostealer logs, with cookie databases, and with active credential markets. The phishing campaign that targets you tomorrow doesn't have to guess what you use. It can pull a high confidence match on which services you've registered for going back a decade.
SC Media's coverage of the post downplayed the novelty—correctly noting that little of this data is new—while still acknowledging that the operational result is a usable, deduplicated phishing list that drops the cost of a campaign by orders of magnitude. The math the Cybernews team ran is grim. If just 0.001% of holders of those 3 billion addresses click a malicious link, that's 30,000 successful infections per campaign.
"ULP Collections" Are the Quiet Tell
The Adkka72424 post mentioned "ULP collections"—URL/Login/Password files harvested from infostealer malware. That's not breach data. That's data exfiltrated in real time from infected machines, often with active session cookies attached.
Infostealer logs are the supply chain that fuels modern phishing as a service operations. A single infostealer victim donates not just their email, but the URLs they were logged into, the saved passwords in their browser, the cookies that bypass MFA, and metadata about their employer. When that gets aggregated into a 6.8 billion line file, the resulting list isn't just email addresses. It's a graph of which people are valid login holders for which services—exactly the targeting input that the AI assisted phishing kits documented in the Bluekit phishing service and the ATHR AI vishing platform consume directly.
"Whistleblower" Branding Is Doing Cover
Adkka72424 posted the dump with a framing message: "your data is public." That's the language of a whistleblower, not a criminal. It echoes the public interest defenses that have followed earlier mass dumps from Collection #1 to the COMB compilation of 3.2 billion records in 2021.
The branding does two things at once. It launders reputation for the actor inside criminal forums, where doxxing style "I'm just exposing the truth" framings buy goodwill. And it complicates the legal posture for downstream consumers of the file—anyone scraping the dump for a phishing list now has a fig leaf in case of prosecution. Several outlets, including Cyber Security Review, repeated the "warning" framing without challenging it.
What Happens to These Lists Next
Phishing operators don't just spam 3 billion addresses at random. The economics don't work and the deliverability is terrible. The lifecycle of a dump like this looks more like the following:
- Segmentation. Operators split the file by domain.
@gmail.comgoes one way.@*.govand@*.eduget prioritized for high value targeting. - Cross reference with existing infostealer feeds. Anyone whose email matches a recent infostealer log gets bumped to the top of the queue—those are the addresses with active cookies and saved passwords.
- Tailored campaigns. Brand impersonation kits like Bluekit cycle Gmail, Outlook, iCloud, and crypto wallet templates. The 3 billion address pool means a campaign operator can afford to send hyper targeted lures to specific service users.
- Tertiary resale. The file gets cleaned, tagged, and sold in smaller "verified" subsets through Telegram channels.
The lifespan of a 3 billion address list is measured in years, not weeks. Phishing volumes attributable to Collection #1 are still measurable in 2026, seven years after that file leaked.
What You Should Actually Do
The reflexive advice is "change your password." That's not the right advice for an email only dump. The right advice is structural:
- Check Have I Been Pwned. The HIBP service from Troy Hunt has historically ingested compilations like this within weeks. Search your email at haveibeenpwned.com and treat any hit on a recent dump as confirmation that your address is on phishing target lists.
- Move high value accounts to passkeys or hardware keys. A leaked email plus a guessable password remains the single most common breach vector. Passkeys eliminate the password from the equation entirely.
- Use email aliasing for new signups. Tools like Apple Hide My Email, Firefox Relay, and SimpleLogin generate per service forwarding addresses. The next time a service gets breached, only the alias leaks.
- Audit your browser saved credentials and clear them. The "ULP collections" feeding files like this come from infostealer malware that grabs whatever the browser kept. A password manager with master password encryption is dramatically safer than browser storage.
- Treat any "your account has been compromised" email as a phishing lure until proven otherwise. The first wave of campaigns off a dump like this almost always uses the dump itself as social proof. Verify by typing the URL of the service, never by clicking a link.
The Honest Takeaway
Adkka72424's compilation didn't expose anything that was truly secret. Most of these addresses have been circulating in pieces for years. What the dump did was lower the price of access. A single 150 GB file with 3 billion verified addresses is now a commodity input for any phishing operation that wants one.
The defensive posture for individuals and companies is the same as it has been for the last decade: assume your email address is public, harden the accounts attached to it, and stop relying on the secrecy of an identifier that 3 billion strangers can also see. Smaller, more targeted leaks—like the 959 Fortune 500 emails ClickUp left in its homepage JavaScript for 15 months—are the targeting fuel that aggregations like Adkka72424's never quite become on their own.